WADA explains how Fancy Bears hackers got into athletes' confidential medical files
World Anti-Doping Agency issues statement detailing how the Fancy Bears hacking group accessed its confidential files, and what it is doing to prevent it happening again

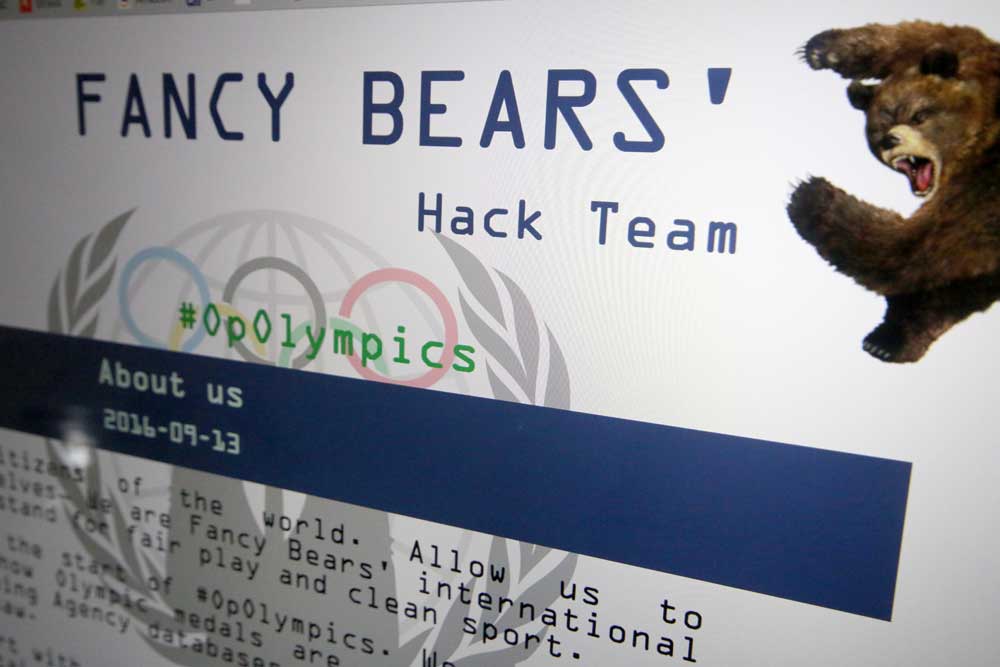
The World Anti-Doping Agency has issued a statement outlining how the hacking group Fancy Bears illegally accessed confidential medical files stored on its computer system.
Fancy Bears have been publishing the hacked data in batches in what WADA has called a 'cheap shot at innocent athletes'. WADA's statement outlines how the hackers got into its system and what it is now doing to ensure the security of its files going forward.
Fancy Bears focussed on accessing athletes' therapeutic use exemption (TUE) certificates, which are issued when an athlete is prescribed a substance on WADA's Prohibited List for a legitimate medical reason. The hacking group – thought to be based in Russia – says that its remit is "exposing the athletes who violate the principles of fair play by taking doping substances".
TUEs for British cyclists Bradley Wiggins, Chris Froome, Laura Trott, Callum Skinner and Steve Cummings have been published since Fancy Bears first started putting them online on September 13. A TUE is not evidence of wrongdoing.
>>> Bradley Wiggins’s and Chris Froome’s medical data released by Russian hackers
"The criminal activity undertaken by the cyber espionage group, which seeks to undermine the TUE program and the work of WADA and its partners in the protection of clean sport, is a cheap shot at innocent athletes whose personal data has been exposed," said the statement issued by WADA on Wednesday.
According to WADA, Fancy Bears used a 'spear phishing' method to gain the password for an account on its Anti-Doping Administration and Management System (ADAMS) created for the Rio 2016 Olympic Games in June for the International Olympic Committee (IOC). The phishing attacks occurred before and during Rio 2016.
The latest race content, interviews, features, reviews and expert buying guides, direct to your inbox!
The ADAMS account was then accessed illegally 'multiple times' by hackers between August 25 and September 12 using account details gained from the phishing attack.
WADA has confirmed that the data published by Fancy Bears so far corresponds to that accessed illegally in the period specified.
As soon as the first batch of TUEs was published by Fancy Bears on September 13, WADA realised that there had been a security breach and reports that it immediately put in place a number of measures. These included disabling the Rio 2016 account and increasing the logging of activity on its systems.
Law enforcement agencies in Canada, where WADA is based, and elsewhere have been part of the investigation.
>>> ‘Athletes should not be required to publicly defend their legitimate use of a TUE’ says WADA
WADA also engaged cyber security firm FireEye Inc to assess the extent of the data breach by Fancy Bears and ascertain what files were removed from its system. According to the statement, only TUEs were accessed and not broader data held on the ADAMS system.
Not all details of its on-going investigation into the security breach have been published, with WADA saying: "It should be noted that WADA’s investigation is ongoing; and so, while the Agency wishes to keep stakeholders informed, it is mindful of the risks of disclosing information that might compromise the integrity of its investigation".

Nigel Wynn worked as associate editor on CyclingWeekly.com, he worked almost single-handedly on the Cycling Weekly website in its early days. His passion for cycling, his writing and his creativity, as well as his hard work and dedication, were the original driving force behind the website’s success. Without him, CyclingWeekly.com would certainly not exist on the size and scale that it enjoys today. Nigel sadly passed away, following a brave battle with a cancer-related illness, in 2018. He was a highly valued colleague, and more importantly, an exceptional person to work with - his presence is sorely missed.
