Fake Strava segments reveal location of secret Israeli military intelligence bases
Israeli disinformation watchdog identifies fake user uploading bogus segments to spy on personnel in top-secret installations


A security breach on Strava has been used to spy on Israeli security personnel at secret military bases, according to FakeReporter, an Israeli disinformation watchdog.
FakeReporter, which uses volunteers and open source experts to crowdsource investigations, says its researchers estimated that a "data mining method" was used to identify at least 100 individuals using Strava while exercising in at least six top-secret installations in Israel.
It claims that a "vulnerability" in Strava allows “suspicious actors” to upload fake GPS files - segments placed inside regions believed to be where sensitive operations were taking place - and collect the data of users.
Article continues below 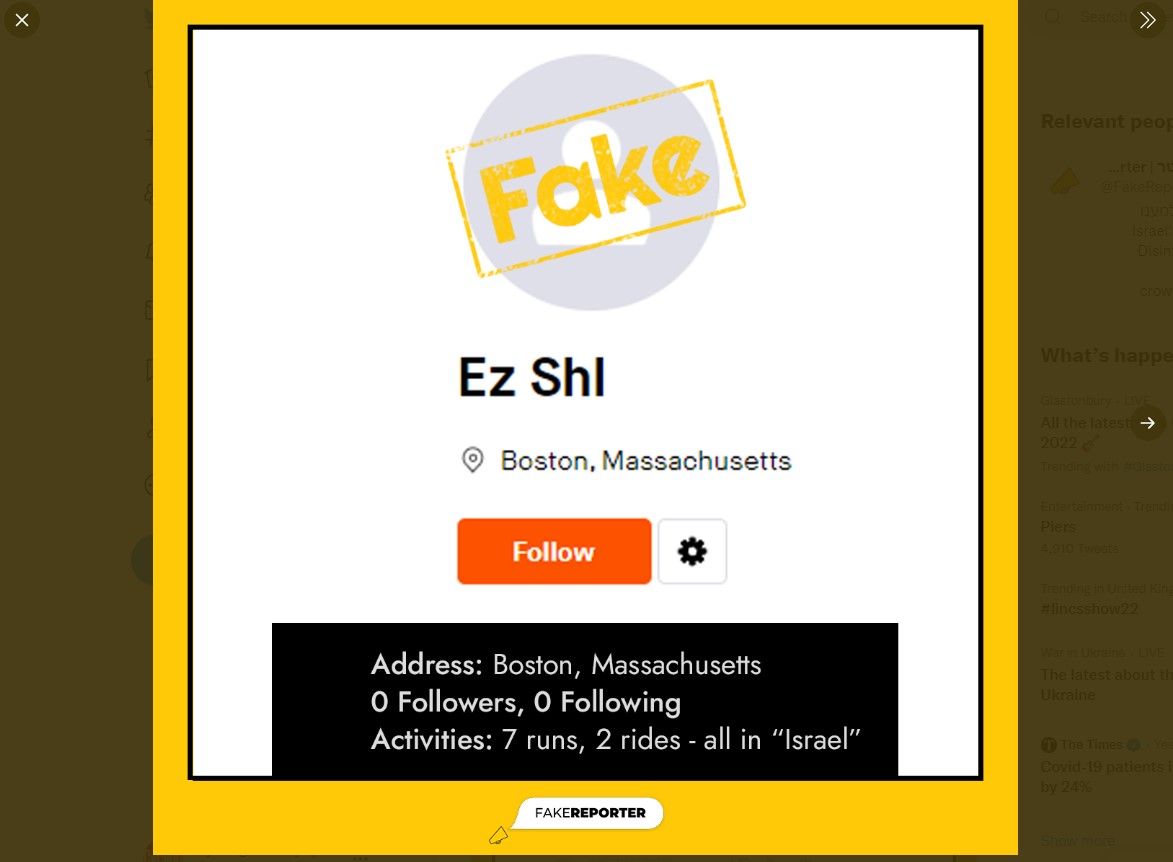
According to Israeli newspaper Haaretz, a fake user, called Ez Shl, uploaded fake running data to Strava to create segments from sensitive Israeli sites in order to reveal the identities of people who had run in those areas. Haaretz says the data uploaded by the user is clearly fake as it shows him or her running long distances in “0 seconds.”
The locations of the sites were saved and marked and the fake user created a small database that included two air force bases, at least two Israeli military intelligence bases and Mossad headquarters according to Haaretz.

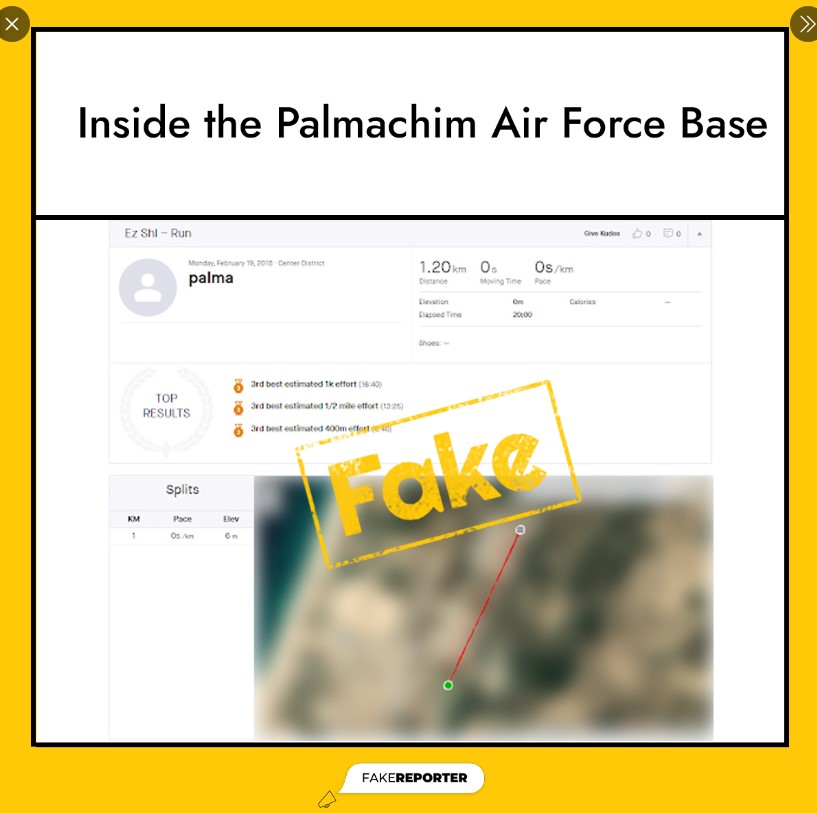
Haaretz claims that among the bases with details exposed were those of the Israel Air Force at Palmachim (above) and Ramat David; among the military intelligence bases was Glilot and another near Jerusalem.
Among the soldiers exposed were over 50 from Palmachim, including officers from an elite unit, and some who also ran routes near Dimona, the site of Israel’s nuclear reactor.
The latest race content, interviews, features, reviews and expert buying guides, direct to your inbox!
FakeReporter informed both Strava and the Israeli authorities. Strava said: “We take matters of privacy very seriously and have addressed the reported issues.” The Israeli defence ministry did not respond.
Achiya Schatz, FakeReporter's director, said in a statement: "Despite past revelations, it does not appear that Israeli security agencies have caught up... although Strava made significant updates to its privacy settings, confused users might still be exposed publicly, even if their profiles were set to 'private'.
"By exploiting the capability to upload engineered files, revealing the details of users anywhere in the world, hostile elements have taken one alarming step closer to exploiting a popular app in order to harm the security of citizens and countries alike."
In 2018 Strava made changes to its global heatmap after the locations of sensitive US military bases including in Syria and Afghanistan were revealed.
From September 2018 its privacy settings were simplified so that profiles and activities could be set to "Everyone", "Followers" or "Only you"
It was also possible to opt out of Flybys - which allowed users to see which other users they had passed or been close to, and it was also possible go opt out of contributing to Metro and Heatmap - something which the exposed Israeli personnel possibly didn't do.
As of 2018 it was also possible to hide portions of your activity map from other users so as not to reveal the exact location of your home, for example.
Simon Smythe is a hugely experienced cycling tech writer, who has been writing for Cycling Weekly since 2003. Until recently he was our senior tech writer. In his cycling career Simon has mostly focused on time trialling with a national medal, a few open wins and his club's 30-mile record in his palmares. These days he spends most of his time testing road bikes, or on a tandem doing the school run with his younger son.
